For years, the cryptocurrency economy has been rife with black market sales, theft, ransomware and money laundering – despite the strange fact that in that economy, practically every transaction is written into a blockchain’s permanent, unchangeable ledger.
New evidence suggests that years of advancements in blockchain tracing and crackdowns on that illicit underworld may be having an effect – if not reducing the overall volume of crime, then at least cutting down on the number of laundering outlets, leaving the crypto black market with fewer options to cash out its proceeds than it’s had in a decade.
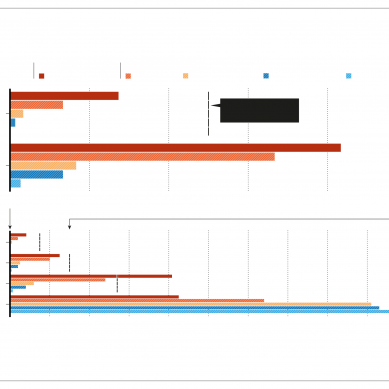
In a portion of its annual crime report focused on money laundering that was published last week, cryptocurrency-tracing firm Chainalysis points to a new consolidation in crypto criminal cash-out services over the past year. It counted just 915 of those services used in 2022, the fewest it’s seen since 2012 and the latest sign of a steady drop-off in the number of those services since 2018.
Chainalysis says an even smaller number of exchanges now enable the money-laundering trade of cryptocurrency for actual dollars, euros and yen: It found that just five cryptocurrency exchanges now handle nearly 68 per cent of all black market cash-outs.
In fact, Chainalysis saw just 542 cryptocurrency deposit addresses receive more than half of the $6.3 billion in total illicit funds it tracked to those cash-out services in 2022, and just four addresses received $1.1 billion of those funds.
That intense narrowing of so-called “off-ramps” for crypto crime is a result of an ongoing government crackdown on crypto money laundering and a sign of additional enforcement on the way, says Kim Grauer, Chainalysis’ director of research.
“It’s shocking to see some of these deposit addresses moving more than a hundred million dollars in illicit funds and still operating when it’s something that’s extremely transparent and easy to see with blockchain analytics,” Grauer says. “So it does seem like a good chokepoint, where we can shut down and profile and – to some degree – eradicate this activity.”
Whether the overall amount of crypto crime rose or fell in 2022, meanwhile, is far from clear: By some measures, Chainalysis’ data has shown that criminal use of cryptocurrency increased last year despite the steep decline in cryptocurrency exchange rates. But those numbers include a huge spike in illegal transactions at sanctioned cryptocurrency exchanges, which may have less to do with a rise in crime than with the US Treasury’s Office of Foreign Asset Control (OFAC) increasingly imposing those sanctions on major players in the crypto underground.
In April of last year, for instance, OFAC sanctioned Garantex, an exchange based in Russia that it says laundered over $100 million in criminal proceeds, including ransomware payments. The year before, it sanctioned two other Russian exchanges, Chatex and Suex, which have since gone out of business.
Just last week, OFAC sanctioned another exchange, Bitzlato and the Justice Department indicted its Russian founder, Anatoly Legkodymov and tore his operation offline.
“You don’t carry out a ransomware attack if there’s no way of converting that ransom into something usable,” says Grauer. “What we’re really seeing OFAC doing, and what we’ve really highlighted, is that the money-laundering off-ramps are what’s facilitating crime. And I think the ongoing crackdown has shown that people understand they’re at a point where there can be meaningful intervention.”
Chainalysis declined to name the five exchanges it says enabled the majority of cryptocurrency money laundering. That’s because, the company says, those exchanges may be the targets of ongoing investigations. (Chainalysis often works with law enforcement agencies in those investigations.)
Further, the exchanges may not actually be aware that they’re enabling that money laundering, since money launderers often take pains to hide the source of their funds before it hits an exchange.
In fact, Chainalysis found that a large chunk of the illicit cash-outs went through two types of intermediaries that might obfuscate criminal funds: Many were traded through “nested services,” essentially exchanges that appear to be independent but actually use a larger exchange to carry out their trades.
In those cases, the nested service, rather than the underlying exchange, is often responsible for complying with “know-your-customer” requirements, even as the larger exchange provides the cash reserves for transactions.
In another growing subset of cases, Chainalysis says, criminals are turning to individual dark-web-based money-laundering services, many of which offer to hide the origin of funds by combining them with other users’ transactions in a “mixer.”
As law enforcement has cracked down on major mixing services in recent years – seizing and tearing offline the mixers Bitcoin Fog and Helix and sanctioning the mixing service Tornado Cash, for instance – more criminals have turned to smaller dark-web services that Chainalysis’ Grauer refers to as “mom-and-pop” mixers, whose distributed nature makes them harder to seize or disrupt.
Despite its reluctance to name the top five money-laundering exchanges in its most recent report, in another report in February of last year Chainalysis did point to a collection of Russia-based exchanges it says have cashed out large sums of criminal proceeds.
While some of the exchanges named in that report have since been sanctioned or gone offline, others – including Cashbank and TETChange – appear to still be active.
When Wired reached out to the US Treasury, an official there declined to comment on any specific exchanges or ongoing investigations. The official, who asked to remain unnamed due to the sensitive nature of sanctions policies that are coordinated between multiple government agencies, also suggested that Chainalysis’ data offered only one incomplete perspective on the crypto money-laundering landscape and that much of the consolidation it describes might simply be due to 2022’s crypto crash and the resulting bankruptcy of several exchanges – particularly more “fly-by-night” ones with looser compliance rules.
But the official also pointed to the Treasury’s own enforcement efforts – along with those of international partners – as an ongoing crackdown that has intentionally reduced options for criminals. “The way you get at money laundering on a broadscale is you slowly whittle down the number of open vulnerabilities. Little by little you make the gaps fewer and fewer, smaller and smaller,” the official says. “If you close up more gaps in the dam, more water flows through those open holes.”
As gradual as that process may be, Chainalysis’ Grauer says it’s a sign that efforts to trace and disrupt the crypto criminal world’s ATMs are slowly but surely having their intended effect.
“We’ve worked to show where the money-laundering gaps are. There are gaps that remain,” says Grauer. “The crackdown is in progress.”
The notorious Russian-speaking cybercriminals grew successful by keeping a low profile. But now they have a target on their backs. The exposure of hundreds of millions of email addresses puts pseudonymous users of the social network at risk.
Some 1,700 spoofed apps, 120 targeted publishers, 12 billion false ad requests per day – Vastflux is one of the biggest ad frauds ever discovered. The infamous, FSB-connected Turla group took over other hackers’ servers, exploiting their USB drive malware for targeted espionage.
Any multifactor authentication adds protection, but a physical token is the best bet when it really counts.
- A Wired report